The Contact Centre solution for delighting your customers.
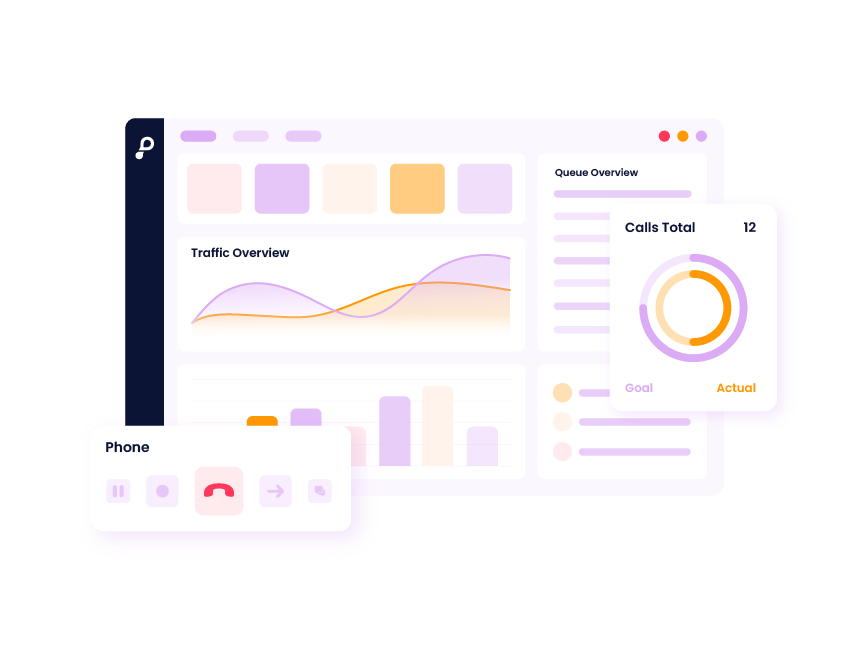
Meet your customers where they are and resolve queries, faster. Our Contact Centre solution empowers your agents to deliver first-class customer support in the right channel, elevating every conversation.
Trusted by Europe's Customer Experience leaders.

Channel Optimisation
Meet your customers where they are.
Customer expectations are higher than ever. Our mission is to ensure you have the right tools to exceed them. The Puzzel Contact Centre solution lets you create consistent customer journeys and meet your customers in the best channel for their query – whether it’s email, web, SMS, voice or social media. Plus, with a single interface and AI-enhanced tools, your agents have all they need to deliver quick, personalised responses.
Key features.





Optimise your contact centre
with powerful add-ons.
Explore some of our extended capabilities and learn how these can enhance your contact centre operations.

Unlock your team's potential with the Puzzel CX ecosystem.
Puzzel Contact Centre is part of the Puzzel CX Ecosystem which combines Contact Centre as a Service with Self-Service Automation capabilities. This helps you consolidate all your contact centre technologies in a single platform, so you can focus on what matters most – providing delightful customer experiences, regardless of channel.
The latest from our blog.
Frequently asked questions.
The Puzzel Contact Centre Solution is a flexible and scalable cloud-based contact centre platform that helps businesses manage customer interactions across multiple channels, including voice, email, chat, and social media. The solution is designed to enhance customer experience and improve agent productivity through intelligent routing, workflow automation, and real-time analytics.
A cloud contact centre solution is a digital customer service platform enabling businesses to manage multi-channel customer interactions efficiently, enhancing customer service and support. Cloud contact centres usually include several channels, such as voice, email, SMS, video, chat, and social media.
The solution improves customer satisfaction by ensuring customers are routed to the right agent quickly using intelligent routing. It also enables customers to interact through their preferred channels and leverages analytics to identify issues and trends in customer behavior.
Puzzel increases productivity through automation and integration features that streamline agent workflows. Key features include:
- Automated task management for prioritizing inquiries.
- Unified interfaces for agents, reducing time switching between applications.
- Integration with CRM systems for seamless information access.
The main benefits include:
- Flexibility: The solution is customizable for businesses of various sizes and industries.
- Scalability: Easily scales up or down based on business needs.
- Omnichannel capabilities: Manages interactions across multiple channels from a unified platform.
- Analytics and Reporting: Provides real-time data insights to improve decision-making.
- Seamless Integrations: Integrates with popular business tools and CRM systems.
Yes, I want my customer care Norwegian style.
Puzzel Contact Centre is part of the Puzzel CX platform which combines Contact Centre as a Service with Self-Service Automation capabilities. This helps you consolidate all your contact centre technologies in a single platform, so you can focus on what matters most – providing delightful customer experiences, regardless of channel












